By suktech24, Sun 2 Feb 2025, Estimated reading time : 7 mins
The software supply chain has become a prime target for cybercriminals. By compromising packages in PyPI and npm, attackers gain a stealthy foothold, executing harmful code upon installation. Datadog’s Q4 2024 research pinpoints two common attack vectors in PyPI, attackers overwrite the setup() function within setup.py, while in npm, they utilize pre- or post-install scripts within package.json.
In this week’s blog post, I’m diving into a critical software supply chain attack highlighted in Datadog’s Q4 Threat Insights report: MUT-8694. This research underscores the increasing threat of malicious packages in popular repositories like PyPI and npm, and how attackers are leveraging these platforms to distribute malware and target developers. Below topics will be discussed:
- Discovery
- Infostealer malware
- Key Findings
- Sigma Rule
- Terminologies
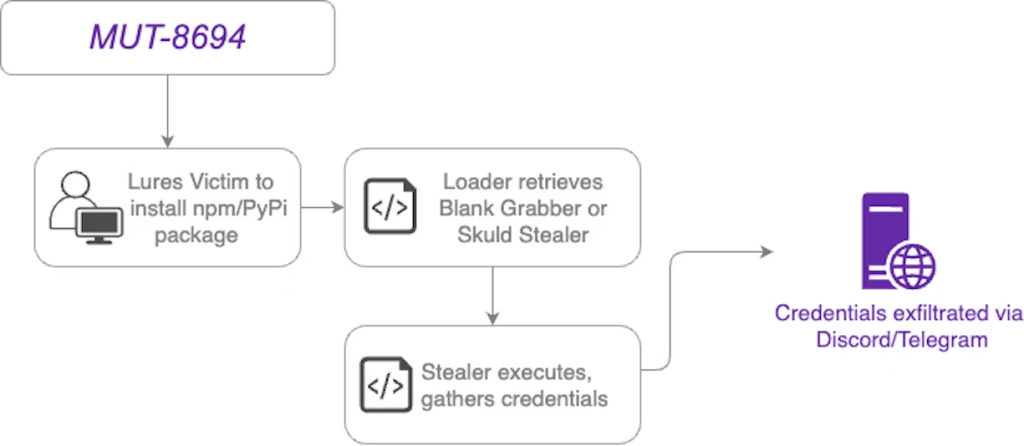
Attack Flow Diagram ( Sourced from datadog)
Discovery
On October 10, 2024, the malicious PyPI package larpexodus was discovered after triggering a GuardDog alert due to its execution of an externally hosted Windows binary. This discovery led to the identification of 42 related malicious PyPI packages, all sharing the same loader code for infostealer malware like Blank Grabber and Skuld Stealer. These packages often used descriptions referencing DLL/API resolution, MuMu Player, or Solara, suggesting a targeting of developers, though not of a specific stack.
Subsequently, on October 16, 2024, GuardDog flagged the npm package nodelogic, which, like the PyPI packages, retrieved and executed obfuscated infostealers from GitHub and repl.it via a post-installation hook. This discovery revealed a larger campaign, MUT-8694, coordinating attacks across both PyPI and npm. While the PyPI packages seemed to target developers generally, the 18 discovered npm packages often referenced Roblox, indicating a focus on Roblox developers.
Package Metadata and others
| Feature | PyPI | npm |
|---|---|---|
| Package Name | larpexodus | nodelogic |
| Version | 0.1 | 1.0.0 |
| Date Published | October 10, 2024 | October 16, 2024 |
| Description | Empty (often misleading, e.g., DLL/API, MuMu Player, Solara) | “Advanced package used for easy API/DLL repair…” (often misleading, e.g., Roblox) |
| Initial Execution | Custom installation code (cmdclass in setup.py) | Post-installation hook (obfuscated JavaScript) |
| Target | General developers | Primarily Roblox developers |
| Number of Packages | 42 | 18 |
| Malware Deployed | Blank Grabber, Skuld Stealer (and likely others) | Blank Grabber, Skuld Stealer (and likely others, obfuscated) |
| Malware Hosting | GitHub, repl.it | GitHub, repl.it (obfuscated samples) |
2. Infosealer Malware
2.1. Blank Grabber
Blank Grabber, delivered as a PE32 executable (often named CBLines.exe) hosted on GitHub (URL no longer valid), is a Python-based infostealer compiled with PyInstaller. It boasts evasion capabilities, targeting a wide range of data, including Roblox cookies, crypto wallets, browser passwords, Telegram sessions, and capturing screenshots and webcam images.
Data exfiltration occurs via Discord webhooks or a Telegram bot. Upon execution, Blank Grabber copies itself to the user’s Temp directory and adds itself to the Windows Defender exclusion list via a PowerShell command, effectively hindering detection. It also gathers geolocation and reverse DNS lookup information about the victim’s IP address using ip-api.com.
2.2. Skuld Stealer
Another malware variant observed in this campaign is Skuld Stealer. Written in Go, Skuld Stealer, like Blank Grabber, has a modular architecture and focuses on targeting Discord users on Windows. Its GitHub repository highlights features such as Windows Defender evasion, virtual machine detection, and persistence mechanisms. Skuld Stealer begins by defining a user-generated Discord webhook URL, which is then used for the exfiltration of stolen credentials.
3. Key Findings
- A staggering 80% of malicious PyPI packages manipulate the
setup()function insetup.pyto execute arbitrary code. - Over 90% of malicious npm packages exploit pre- or post-install scripts within
package.json. - MUT-8694 uses a series of malicious packages to deliver infostealer malware to Windows users, and makes use of legitimate services, such as GitHub and repl.it, to host additional payloads.
- The malware deployed in this campaign, including variants like Blank Grabber and Skuld Stealer, is designed to exfiltrate sensitive data such as credentials, cookies, and cryptocurrency wallet information.
Sigma Rule
NOTE : This detection sigma rule was developed for my personal learning purposes.
title: Blank Grabber - Data Exfiltration & Persistence
id: a3e9c5f1-2e1a-3c6-bd68-f4792c6f66a29
description: |
Detects Blank Grabber malware creating RAR archives, exfiltrating data via Telegram, and disabling Windows Defender, as part of a software supply chain attack leveraging malicious PyPI packages.
status: developed_for_personal_learning_purpose
author: suktech24
date: 2025-02-02
tags:
- malware
- data exfiltration
- persistence
- infostealer
- Blank Grabber
- threat hunting
references:
- "https://www.datadoghq.com/blog/supply-chain-attack-npm-pypi-mut-8694/"
- "https://securitylabs.datadoghq.com/articles/2024-q4-threat-roundup/"
mitre:
tactic:
- TA0010, Exfiltration, https://attack.mitre.org/tactics/TA0010/
- TA0005, Defense Evasion, https://attack.mitre.org/tactics/TA0005/
technique:
- T1560.001, Archive Collected Data: Archive via Utility, https://attack.mitre.org/techniques/T1560/001/
- T1020 # Automated Exfiltration
- T1071.001 # Application Layer Protocol: Web Protocols (Telegram Bot)
- T1562.001 # Impair Defenses: Disable or Modify Tools
logsource:
category: process_creation
product: windows
service: sysmon
detection:
selection_rar_exfiltration:
Image|endswith:
- "rar.exe"
CommandLine|contains:
- "-hp" # Password-protected RAR archive creation
selection_telegram_exfiltration:
Image|endswith:
- "powershell.exe"
CommandLine|contains:
- "bot7546407054"
- "api.telegram.org/bot"
selection_defender_disable:
Image|endswith:
- "powershell.exe"
CommandLine|contains:
- "Set-MpPreference -DisableRealtimeMonitoring $true"
- "Set-MpPreference -DisableScriptScanning $true"
- "Set-MpPreference -SubmitSamplesConsent NeverSend"
selection_persistence:
Image|endswith:
- "powershell.exe"
CommandLine|contains:
- "Copy-Item -Path C:\\Users\\*\\AppData\\Local\\Temp\\CBLines.exe"
- "-Destination C:\\Users\\*\\AppData\\Local\\Temp\\"
condition: >
selection_rar_exfiltration or
selection_telegram_exfiltration or
selection_defender_disable or
selection_persistence
level: critical
falsepositives:
- Legitimate use of Telegram API for automation.
- Admins archiving files for backups.
fields:
- Image
- CommandLine
- ParentImage
- UserYou can also visit https://github.com/sukTech24/detection_rules repo
Terminologies
- MUT-8694
- Uses a series of malicious packages to deliver infostealer malware to Windows users, and makes use of legitimate services, such as GitHub and repl.it, to host additional payloads.
- Intends to compromise developers
- Mysterious Unattributed Threat – MUT
- MUT (mysterious unattributed threat) designation to track clusters unattributed to a known threat actor.
- Blank Grabber is an infostealer malware designed to capture sensitive data. While initially created to target Windows systems, it can be reprogrammed to target other operating systems, too.
- larpexodus package
- Execute a powershell command to download and execute ==> Windows PE32 Binary from github[.]com/holdthaw/main/CBLines.exe (404)
- Typosquatting (URL Hijacking/ Domain Mimicry/Sting Sites/Fake URLs)
- Typosquatting is a type of social engineering attack which targets internet users who incorrectly type a URL into their web browser rather than using a search engine. Typically, it involves tricking users into visiting malicious websites with URLs that are common misspellings of legitimate websites. Users may be tricked into entering sensitive details into these fake sites.
- Windows Defender exclusion
- powershell -Command Add-MpPreference -ExclusionPath ‘C:\Users\\AppData\Local\Temp\CBLines.exe’
- Add-MpPreference
Add-MpPreferencecmdlet modifies settings for Windows Defender. Use this cmdlet to add exclusions for file name extensions, paths, and processes, and to add default actions for high, moderate, and low threats.- This command adds the malware’s executable to the Windows Defender exclusion list, preventing the EDR from scanning the file and identifying it as malware.
- Set-MpPreference
- Configures preferences for Windows Defender scans and updates.
- Malicious packages of MUT-8694
- Blank Grabber
- CBLines.exe (PE32 executable)
- Skuld Stealer
- Written in Go and targets Discord users on Windows
- Blank Grabber
- mpcmdrun.exe (Microsoft Protection Command Line Utility)
- It is a command line tool used to manage and interact with Windows Defender (Microsoft Defender Antivirus) in Windows.
- PyPI
- Python Package Index (PyPI) is a repository of software for the Python programming language.
- Supply chain attack
- A supply chain attack is a type of cyberattack that targets a trusted third-party vendor who offers services or software vital to the supply chain.
- Software supply chain attacks inject malicious code into an application in order to infect all users of an app, while hardware supply chain attacks compromise physical components for the same purpose.
- Today, the average software project has 203 dependencies. If a popular app includes one compromised dependency, EVERY BUSINESS that downloads from the vendor is compromised as well, so the number of victims can grow exponentially.
References
- Datadog threat roundup: top insights for Q4 2024, Jan 24 2025, https://securitylabs.datadoghq.com/articles/2024-q4-threat-roundup/
- MUT-8694: An NPM and PyPI Malicious Campaign Targeting Windows Users, Nov 22 2024, https://securitylabs.datadoghq.com/articles/mut-8964-an-npm-and-pypi-malicious-campaign-targeting-windows-users/
- Blank Grabber, https://nordvpn.com/cybersecurity/threat-center/blank-grabber/
- Typosquatting, https://www.kaspersky.com/resource-center/definitions/what-is-typosquatting

Leave a comment